Introducing Phishing Frenzy
A couple weeks ago I presented at this years Derbycon on an email phishing platform that I have been working on. The web application is geared towards penetration testers who want to help streamline the creation and management of email phishing campaigns. The application is written in ruby on rails and is available for download on the Github repository: Phishing Frenzy.
For those of you who came out to my presentation, I appreciate you all getting up so early (Saturday 9am) to hear my talk. Those of you who missed the talk I went over some of the features of Phishing Frenzy and launched a live phishing simulation. You can see the recording below thanks to irongeek. If your looking to see just the demo, fast forward to 11:52.
Phishing Frenzy: 7 Seconds from Hook to Sinker
Phishing Campaigns
I briefly want to go over some of the features that Phishing Frenzy has to offer, including campaign creation, customization, and execution:
Template Management
Once you’ve setup a phishing scenario that works with Phishing Frenzy you can reuse them for all future campaigns. Phishing Frenzy also offers the ability to backup and restore templates. This allows the community to share phishing scenarios with everyone else. To share a Phishing Frenzy template you can submit a pull request to: https://github.com/pentestgeek/phishing-frenzy-templates
Reporting
Phishing Scenario
This phishing scenario that I demonstrated at Derbycon is available as part of the Phishing Frenzy install. I typically make the email look like it came from someone within the company who is an authoritative figure. The email states that everyone should test their passwords to ensure they are in compliance with the company policies.
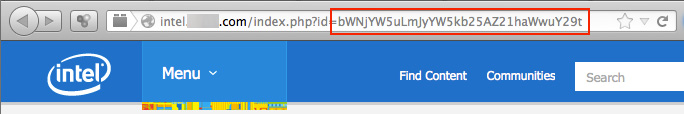
Once the user clicks on the phishing URL, they are directed to our fake Intel Password Checker website. The idea is that any passwords entered into the box will be harvested by us the pentester. You may notice that we are not asking for the users name or username in this scenario, and that is because we already have it.
Using a little PHP magic we can use the $_GET function to pull the base64 encoded email address from id parameter within the url. This way we know the email address and the password entered into the website
Demonstration
Here is a high level overview of how Phishing Frenzy can be used to launch an email phishing campaign.
Outro
This application is currently in beta stages, and needs more QA time. Please try out the software and let me know how it can be improved. If you would like to get involved with the project, please submit a pull request with your code changes or additions.
If you have bug fixes, issues or enhancements for Phishing Frenzy, please submit a ticket using Github. The repositories and install instructions can be found:
- https://github.com/pentestgeek/phishing-frenzy
- https://github.com/pentestgeek/phishing-frenzy-templates
Stay tuned for more documentation and tutorials on how to leverage Phishing Frenzy.
Happy Phishing!
Share this article
Leave a Reply
Share This
Recent Posts
- Playing With the New Burp Suite REST API
- Burp Suite 2.0 Beta Review
- Attacking Palo Alto Networks PAN-OS ‘readSessionVarsFromFile()’
- GPG Errors While Updating Kali Linux
- Installing Kali NetHunter on HTC Nexus 9
Subscribe To Our Mailing List
The Ultimate Burp Suite Training Program
Learn Network Penetration Testing
Penetration Testing
Categories
- AWBS
- Burp Suite
- Definitions
- Forensics and Incident Response
- Information Gathering
- Metasploit
- Penetration Testing Tutorials
- Phishing
- Presentations
- Tools
- Web Applications
- Wireless



zeknox
Thanks very much for this. i’ve been able to setup it up and got smtp working and all,..still a bit sketchy on the apache ( vhost ) setting ish. correct me if im wrong but pf automatically creates vhosts for the phishing site right? im almost there Boss…hopefully i should launch attack ( authourised ) today. How-to guide on vhost setup in respsect to PF would be nice . Thanks once again for this effort. I appreciate and Thank you to all the open source guys and projects out there..your model wins and is forever my model. Thank you.
Please I am not a programmer, I am a network support staff but i am interested in launching this campaign for our small office. How can i just download the application only. Thank you
Everything you need to know about getting up and running can be found over here: http://www.phishingfrenzy.com/resources/
Hey Zeknox. That’s awesome! Thank you so much. Looking forward to it.
My current system is Kali Linux.
Thanks again.
loved the presentation and I love this tool. I am dying to get it up and running. Just one question.. Are you planning on releasing a more how-to for dummies installation guide. I have gone through your readme instruction file but I am stuck on the “Ruby on Rails Configure DB” part. I have no previous experience with ROR’s so I am lost.
If not, I’ll keep Googling away until I get it. ?
Thanks for your awesome site and the work that you share with us.
Chris-
I will be posting more tutorials soon. I’ll try to put together an installation video showing how to setup PF on a fresh OS. If you have any preference on a Linux distro to demonstrate the install on, let me know. Stay tuned…
Very nice tool. Thanks for sharing with the community.