Posted By:Royce Davis - 2/7 - Pentest Geek
Attacking Palo Alto Networks PAN-OS ‘readSessionVarsFromFile()’

A really cool CVE for attacking palo alto networks PAN-OS was published near the end of last year CVE-2017-15944. Just last weak Philip Pettersson created a Metasploit Module to take full advantage of this bug and achieve remote code execution!
Read More
GPG Errors While Updating Kali Linux

I often run into the same GPG errors while updating Kali Linux’s apt-get repositories. The fix is simple enough but I seem to always end up Googling for longer than necessary so I wanted to place the working steps in a single place where I could have them when I undoubtably run into this issue again in the future.
Read More
Installing Kali NetHunter on HTC Nexus 9

Everything you need to begin installing Kali NetHunter can be purchased on Amazon. The only real requirement is of course a supported Android device however this guide also makes use of the keyboard folio which should be considered a necessity if you plan to do any real work on the tablet as well as an OTG cable for plugging in an external WiFi card.
Read More
Website Use Policy
Please read these Terms of Use ("Terms") carefully before using the https://www.pentestgeek.com website operated by Pentest Geek. Your access to and use of the website is c... Read MorePrivacy Policy
This privacy notice discloses the privacy practices for Pentest Geek and our website; https://www.pentestgeek.com. This privacy notice applies solely to information collected ... Read MoreThank You
Thanks again for your purchase! You're account needs to be verified before you can continue. Please click on the link within the email address we just sent you to complete your purchase. Once you have verified yo... Read MoreRecovering Passwords From Hibernated Windows Machines

A friend of mine recently asked if I could help them by recovering passwords from an old Windows laptop. Nothing nefarious here just a common scenario we’ve all been in before. They hadn’t used the system in quite some time and couldn’t recall the password to log in.
Read More
Building A Virtual Pentest Platform
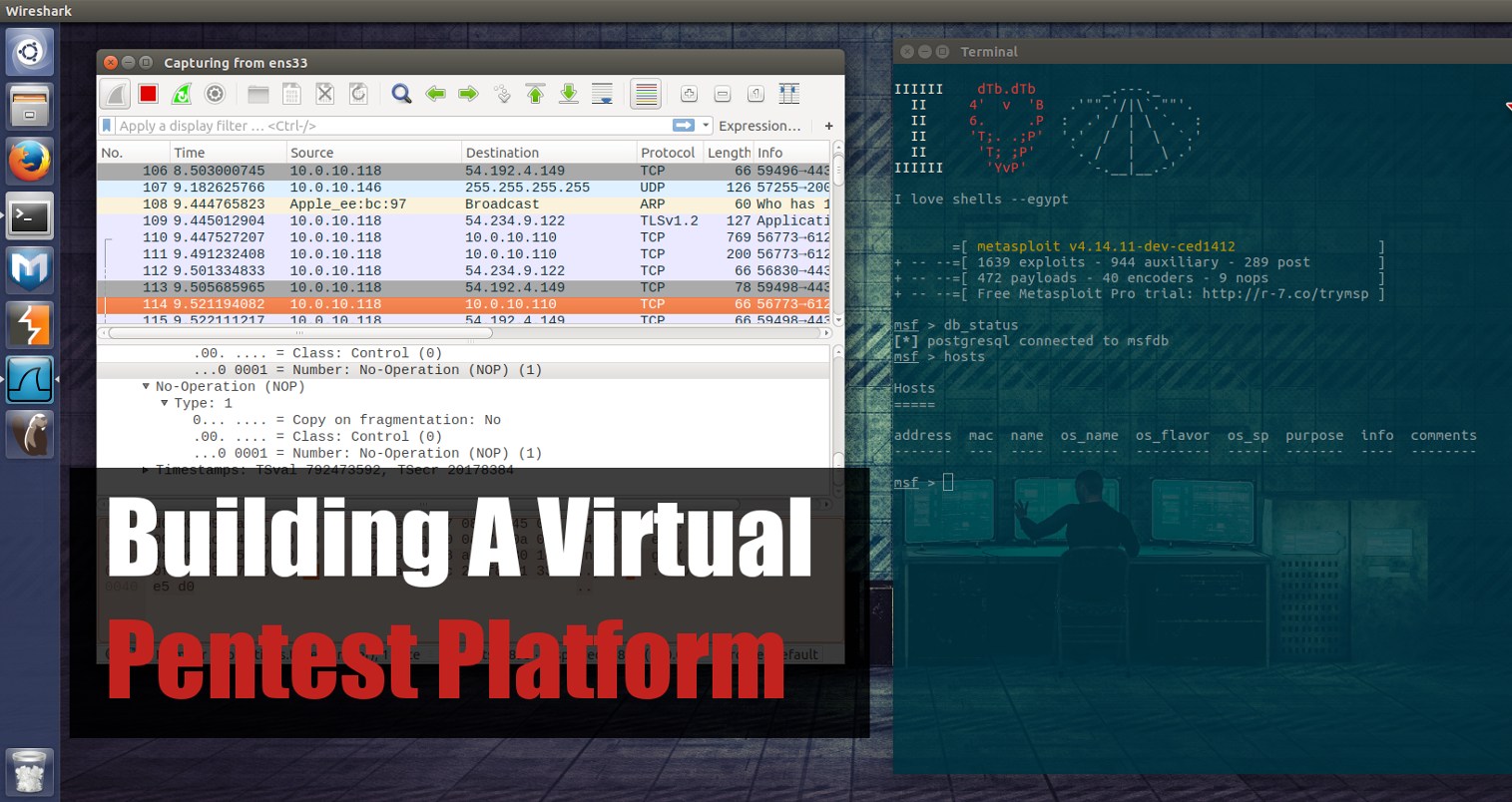
Course Description
In this beginner course you will learn the necessary steps to building a virtual pentest platform capable of performing thorough network security assessments. Start off with a vanilla Ubun... Read MoreShare This
Recent Posts
- Playing With the New Burp Suite REST API
- Burp Suite 2.0 Beta Review
- Attacking Palo Alto Networks PAN-OS ‘readSessionVarsFromFile()’
- GPG Errors While Updating Kali Linux
- Installing Kali NetHunter on HTC Nexus 9
Subscribe To Our Mailing List
The Ultimate Burp Suite Training Program
Learn Network Penetration Testing
Penetration Testing
Categories
- AWBS
- Burp Suite
- Definitions
- Forensics and Incident Response
- Information Gathering
- Metasploit
- Penetration Testing Tutorials
- Phishing
- Presentations
- Tools
- Web Applications
- Wireless



